Trojans sit tight and wait
Tuesday, August 30, 2016
Trojans operate like spies in enemy territory. For a Trojan, as for every professional spy, it is important to infiltrate a system without being detected and to remain there undetected for as long as possible. To achieve this, malware commonly delays its activities; rather than engage in malicious activities as soon as a system’s been infected, criminals wait until the user is likely to have forgotten what websites they’ve visited and what programs they’ve installed.
In addition, by postponing their activities, some malicious programs bypass the mechanisms of heuristic analysis used by anti-viruses and other debugging tools like "sandboxes". If a program launched by a user does not show any signs of malicious activity for a long period of time, the installed anti-virus may assume that the program is safe.
A "sandbox" is an isolated virtual environment used by anti-viruses to monitor unknown or suspicious applications.
In order to identify attempts being made by anti-viruses to detect them, Trojans often perform scans of the registry, the headers of windows opened in the system, and the names of processes and programs, which allows it to get a sense of the virtual environment. If it detects that the environment is "hostile", the Trojan activates a timer and "falls asleep" for some duration of time.
Так, Trojan.Encoder.263, a dangerous Trojan that encrypts user files and demands a ransom for them, waits 20 minutes after its initial launch before commencing with its activities in an infected system, a delay that is likely long enough to get the potential victim to drop their guard.
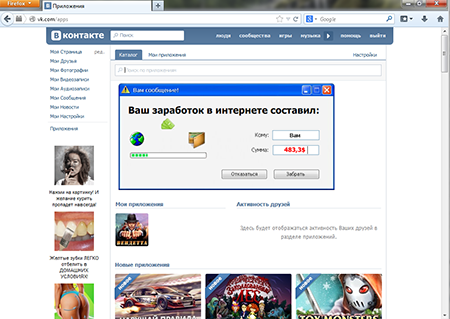
Another typical delayed-action Trojan is Trojan.Triosir.1, which is designed to display annoying ads to users by substituting web content. This Trojan is distributed along with programs of varying degrees of usefulness—for example, with an application that lets you take screenshots and immediately share them with your friends online. However, along with the program, the installer copies several malicious browser plugins onto the disk that remain in the system even after the core software has been removed. To lull the user's vigilance, the malicious components of Trojan.Triosir.1 use a timer set for three days. At the end of that period, the Trojan starts displaying various ads in the browser window; and the user starts finding it hard to determine what’s behind this annoying phenomenon.
Soon virus writers creating malware for the Android mobile platform were adopting the know-how of virus writers targeting Microsoft Windows users. For example, Android.MulDrop.67, which is designed to extract and install other malware on the target device, was spread through different applications on Google Play in the guise of seemingly harmless games. To lull the user's vigilance, virus writers gave this Trojan the option to either implement its malicious features immediately or to delay its malicious activity for 24 hours. #Trojan #Android
The Anti-virus Times recommends
Even if nothing suspicious appears to be happening in your system, it could still be infected. Do not disable the anti-virus protection, and don’t forget to perform a periodic disk check with your anti-virus scanner.


![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
12:38:24 2018-07-15
Mr.Pr
12:31:20 2016-08-30