False evidence
Wednesday, June 5, 2019
You’ve probably seen films where false evidence is planted to incriminate a character. The same can be done in the digital world. It may even be easier.
While staying in his summer residence in Lamy, Czech president Miloš Zeman discovered files containing child pornography on his computer. The security experts involved in the subsequent investigation discovered that the files were uploaded to the hard drive by an unidentified hacker using an American IP address.
The incident didn't tarnish the president's reputation (as far as we know), but things don't always end so well.
What can you do to make sure that nothing strange or illegal will ever be discovered on your computer?
- Don't let just anyone access your computer. If someone does need to access your system, create a guest account with restricted permissions, and delete it as soon as it’s no longer needed.
- Install security updates in a timely manner—this will prevent attackers from hacking into your system by exploiting known vulnerabilities.
- Use a strong password (preferably, a unique one). We believe that the reason for doing that is quite obvious.
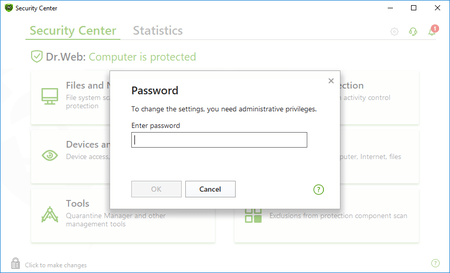
- Set a different password to protect your security software.
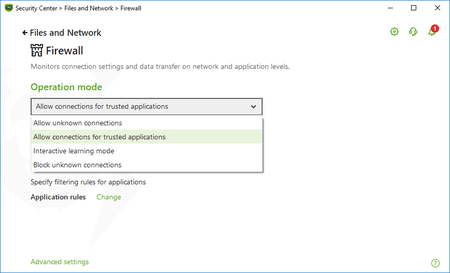
- Use the Dr.Web Firewall to block remote access to your computer via the ports you don’t use (we’ve already explained how this can be done more than once).
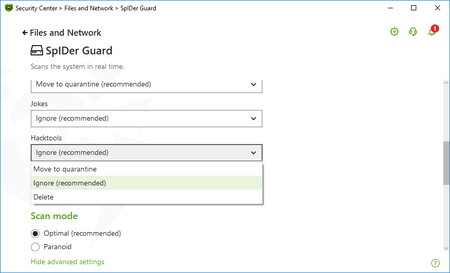
- In the Dr.Web component settings, enable the option "Move to quarantine" for the hack tools category.
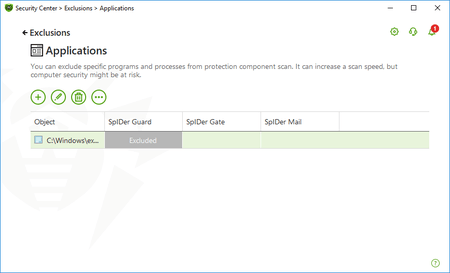
- If you use such a program, add it to the exceptions list.
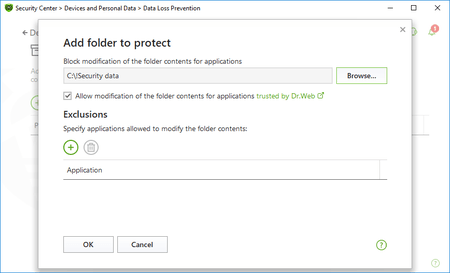
- And, finally, use the Data Loss Prevention component to block programs that are not on your allowed list from accessing your files and folders.
And a final point.
About a year ago, someone uploaded child pornography to my computer. I immediately contacted security experts in Prague and told them that we needed to file a complaint to bring the perpetrators to justice before the data was deleted.
Before you delete the data, try to find out who is responsible—otherwise, they may attack again.
The Anti-virus Times recommends
Unfortunately, modern technologies allow perpetrators to inflict damage with little effort. Therefore, we must do everything we can to make their task as difficult as possible.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
razgen
01:20:32 2019-06-06
Шалтай Александр Болтай
19:29:14 2019-06-05
Татьяна
18:37:13 2019-06-05
Toma
17:19:57 2019-06-05
Masha
14:21:54 2019-06-05
Dmur
12:59:58 2019-06-05
EvgenyZ
08:56:57 2019-06-05
Неуёмный Обыватель
08:15:11 2019-06-05
Пaвeл
07:32:12 2019-06-05