You have a new encrypted message
Thursday, August 4, 2016
Edward Snowden's revelations made the public aware of the fact that government secret services may be collecting and analysing the contents of their mailboxes, instant messages, and phone calls. Protecting customer data from this kind of monitoring became a top priority for many telecom providers, and news of the various data encryption technologies being adopted by them began appearing on a regular basis.
For example:
The smart phone uses 265-bit AES-encryption (chip-to-chip) for data transfer and storage. This feature can be enabled by toggling on a switch on the handheld’s back panel.
https://tech.onliner.by/2016/06/01/solarin
The messenger WhatsApp ensured that encryption was enabled by default for all its customers.
https://lenta.ru/news/2016/04/05/whatsappencrypt
For all of its users, Twitter announced in its blog that it had begun to use HTTPS encryption by default. Use of this secure protocol will ensure that data transferred by users remains secure, particularly when using an unprotected connection, such as a Wi-Fi hotspot in a cafe.
http://ria.ru/science/20120214/565973390.html#ixzz4CU7es2uc
Yandex.Mail started using SSL/TLS encryption for inbound and outbound mail as well as for communications with Gmail users. However, mail on Yandex.Mail’s servers is stored unencrypted. According to company representatives, they use something different to protect the data on their servers, and the text in emails is automatically analysed to detect spam, or to highlight certain text fragments using a context-based interface (e.g., if the message contains airline ticket data).
https://tjournal.ru/p/yandex-mail-encryption
The owners of Viber, an instant messaging and VoIP app, announced that they would introduce the end-to-end encryption that subsequently became available in the updated version of the program (version 6.0) for Android, iOS, PCs, and Mac OS.
http://www.cnews.ru/news/top/2016-04-25_viber_zashchitil_700_mln_polzovatelej_ot_spetssluzhb
Companies—those that understand today’s realities and are obliged to comply with the laws of the country in whose jurisdiction they reside—claim that under no circumstances will user data be accessible to government agencies. Such claims do improve their business image. And, they are music to the ears of the average person who is anxious to avoid any hypothetical surveillance. But, in truth…
Lavabit was a free webmail service striving to protect the secrecy of its users' messages .
On August 8, 2013, Lavabit was closed down. The site's main page displayed the following message from the service's founder and owner Ladar Levison: "My Fellow Users, I have been forced to make a difficult decision: to become complicit in crimes against the American people or walk away from nearly ten years of hard work by shutting down Lavabit. After significant soul searching, I have decided to suspend operations".
Do all company owners act in a similar fashion?
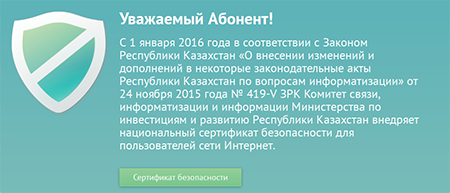
The Internet service providers Beeline and Kazakhtelecom comply with the Republic of Kazakhstan's communications law and replace website certificates with the national security certificate issued by the Communication and Information Committee of the Investment and Development Ministry of the Republic of Kazakhstan. Since January 1, 2016, they have been analysing all TLS traffic.
Internet service providers must obey the law!
But let's take a look at the communications privacy problem from another angle. Communications service providers suggest that a message or file should remain encrypted all the way from the sender to the recipient. The decryption key is only available to the recipient, so the service owner can't transmit it to a third party even if authorities were to demand that they do so.
And that would seem to be OK. But, the problem is that government agencies seldom collect data about ordinary users. Meanwhile, cybercriminals are out to do exactly that. While “man in the middle” traffic monitoring can occur, such attacks are more likely to fall into the category of advanced persistent threats (APTs) that require an understanding and use of sophisticated technologies. Little is known about these attacks, and they occur far less frequently than website- or email-borne infections on the PCs and handhelds of ordinary users which number in the millions.
And, in the case of infection (or if the user's password is stolen), it turns out that even encrypted data is completely unprotected.
In addition to keylogging and special screen-scraping software, the hacker used many metasploit modules and thoroughly examined the files stored on their computers. Fisher also discovered TrueCrypt volume in Pozzi’s system, and patiently waited for him to mount it, so that he could copy data from it. The encrypted volume contained a text file with many passwords.
The Anti-virus Times recommends
- There exist significant risks and “hyped-up” risks—those that are theoretically possible but unlikely to occur. Large businesses must take the latter into account, too. However, for ordinary law-abiding users, the risk of becoming a surveillance target for a secret government service is very low. Yet they are at high risk of having hackers seize control over their accounts or devices.
- Doctor Web protects product updates while they are in transfer, and can protect the exchange of data between anti-virus components, but this is only necessary because criminals are always eager to prevent the anti-virus products of users from receiving updates.


![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
15:21:24 2018-07-23