A website as the weakest link
Thursday, July 21, 2016
One of the most common ways for malware to get onto PCs and handhelds is through downloads from websites; that’s in addition to via infected emails and removable media.
Important! To infect a computer or a handheld, it’s often enough merely to visit a certain website—criminals don't even need to trick you into downloading something!
In this issue we won't be discussing special bogus sites users can land on by accidentally clicking on a banner, or because of web spoofing or some other technique used by criminals. Let's talk about how malware gets onto regular, legitimate websites.
To start distributing malicious programs from a site, criminals first need to gain control over it.
After that they infect a particular web page, and all the pages of one or more sites that are administered under the account that has been compromised. Worms exist that target popular content-management systems. Some malicious programs find all the pages on a disk and add JS code to them. By doing this, attackers can pursue various goals. For example, in addition to offering malware for download, they can change the server configuration files so that under certain conditions, site visitors will be redirected to a malicious site designed to accomplish other tasks.
How do attackers usually gain access to websites?
By exploiting vulnerabilities. Yes, websites can be vulnerable too! Most sites we work with have loopholes.
- Over 60% of web services or APIs for mobile applications contain at least one severe vulnerability through which their databases can be compromised;
- 35% of sites that are vulnerable to XSS attacks are also vulnerable to SQL injections and XXE attacks;
- 23% of sites contain the POODLE vulnerability, and only 0.43% are vulnerable to Heartbleed exploits;
- There has been a five-fold increase in the number of incidents involving the exploitation of severe vulnerabilities (e.g., those involving SQL injections) during RansomWeb attacks;
- 79.9% of web servers use poorly configured or insecure http headers;
- current updates and service packs are installed on only 27.8% of web servers.
High-Tech Bridge releases web security trends of the first half of 2016
https://www.htbridge.com/news/web-security-trends-of-the-first-half-of-2016.html
How are these vulnerabilities exploited, and how do they endanger website visitors?
- SQL-injection vulnerabilities enable criminals to access website database information that the developers of the site meant to keep secret (such information allows the administration panel to be accessed without a password, for example), or alter the stored data (e.g., delete a table or alter text).
- With Code injection, attackers can use data submitted by a user to introduce executable code.
- CSRF (Cross-Site Request Forgery, also XSRF), the most dangerous type of attack, is when an attacker tries to force the browser to send a query to the target server without user consent. As a result, a hacker can perform a variety of actions on behalf of other registered users on the vulnerable site.
- XSS, or cross-site scripting vulnerabilities, enable criminals to exploit a flaw involving the verification of content delivered to a client-side browser. Thus attackers can alter a site's look and feel. You may recall that malicious files written solely in JavaScript already exist.
And, of course, the old-fashioned way of gaining entry hasn’t gone away either: weak or rarely updated passwords.
Furthermore, passwords transmitted over insecure channels can be intercepted by a third party.
Attackers can also gain unauthorised access to a site when the server is poorly configured or during DDoS attacks.
The Anti-virus Times recommends
If you are a website owner:
- Use strong passwords to access your CMS.
- Never use the same password for different sites and services, and change them regularly—a password can be compromised in a data leak and you may remain unaware of it for quite some time.
- Access your site's CMS over a secure channel, especially if you use a wireless network.
- If you have received a password from someone (e.g., a web developer), change it immediately.
- Access to a site may be limited by making it available only to a few addresses—in this case an attacker simply will not be able to login to the site. Exceptions (working from home, while away on business, etc.) should always remain exceptions, and for those periods, you should specify the duration, time of day, addresses, and names of users who are allowed to access the site management system. To improve security, you can also introduce CAPTCHA verification or two-factor authorisation.
- Install updates for the software you use.
- Make sure that the computer from which you control your site is protected by an anti-virus.
- Scan site files with an anti-virus regularly.
- When administering a server, employ token authorisation in addition to a password.
If you are an ordinary user:
- Do not open URLs received from a third party. It sounds straightforward, but it works!
- When you have finished all your site management tasks, log out. Criminals can use an open session to gain access to the site without taking advantage of any exploits.
- Use a different browser or private or anonymous mode to visit important sites (ideally, you should use a separate browser for each site, or—even better—a separate computer).
- Remember that most sites you visit have vulnerabilities. A site that was secure yesterday can pose a threat to all its visitors today.
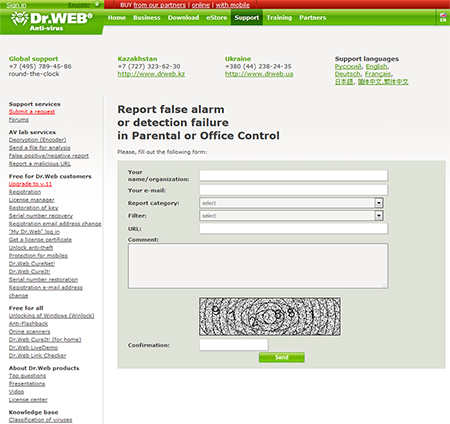
Should you discover a compromised site, notify its administrator and companies that make security-related products.
https://support.drweb.com/new/urlfilter/?lng=en
Select a request category, and specify other information. Provide additional information, if necessary. How did you learn about the site's malicious behaviour?
Thanks for your help in the fight against fraudsters!


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
07:15:50 2018-07-21