Make it a habit to verify, verify, verify
Tuesday, July 19, 2016
Few people are aware of the fact that Android is not an operating system, and, by the way, neither is Linux. Google develops new versions of the Android platform and supplies it to its partners who then tailor it for their needs. As a result, there is an Android 5.1 from Samsung, an Android 5.1 from ASUS, etc. With the device market as fragmented as it is (we discussed this at length in the issue "More Androids, less security"), Android software developers can only support devices produced by popular manufacturers and aren’t physically capable of testing their applications on all smartphones and tablets. But this problem is solvable, at least theoretically.
The worst thing is that, in the absence of a single OS, no centralized system exists for releasing and distributing Android security updates.
Duo Security statistics indicate that 68% of smart phones and tablets powered by Google’s OS are likely to receive updates. But, as of April 30, 2016, the latest available patches were installed on only 25% of the devices for which those patches were intended.
Every third Android smartphone had not received updates since the beginning of this year, which means that these devices are carrying at least 24 known vulnerabilities.
Google is not solely responsible for releasing and distributing updates—device manufacturers use information about vulnerabilities to release and deliver their own updates. Sixty-two percent of the devices that can receive updates are manufactured by Samsung, but only 15% of them have received patches for the most recently discovered vulnerabilities. Even Galaxy devices run outdated versions of Android.
https://duo.com/blog/thirty-percent-of-android-devices-susceptible-to-24-critical-vulnerabilities
The results are sad: Users aren’t getting update notifications and consequently believe that their devices are secure. But that’s completely untrue!
Even back in 2011, there were malicious Android applications exploiting software vulnerabilities in order to elevate their privileges and install and remove software without user consent. These malicious programs, which included Android.DreamExploid and Android.Gongfu, are distributed with altered versions of legitimate applications
The Internet is full of recommendations encouraging users to install updates for the operating system and all the applications they use. People assume that they only need to exercise caution when choosing to install applications and that it’s always safe to install updates for those applications.
However, cybercrime technologies are evolving…
Updates are already being used as a way to introduce malware onto devices! There are known incidents of programs bearing no malicious payload being made available on a particular software portal and then acquiring malignant features later as they were updated.
The Anti-virus Times recommends
- An anti-virus on a handheld should always be kept up to date.
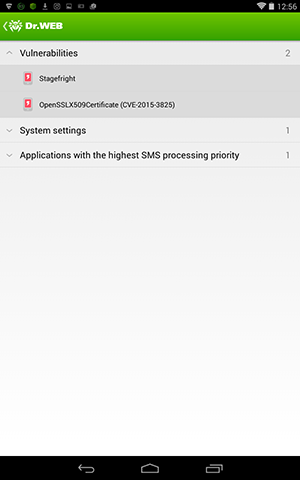
Use the Security Auditor in Dr.Web Security Space for Android to determine how concerned the manufacturer of your device is with regards to its security. The auditor will check your handheld for vulnerabilities.
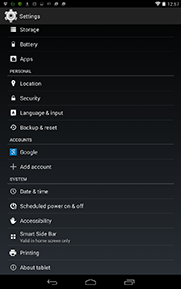
• Should the Dr.Web Security Auditor discover any, check whether there are any security updates you need to install. Go to Settings, select About and choose System update. Then choose the option to check for updates now.
If the update feature is unavailable, it means that your device doesn't support OTA updates. If that's the case, go to the support section of your device manufacturer's site and download the update manually. This usually concerns handsets that run legacy versions of Android.
If security patches for known vulnerabilities haven't been installed on your smartphone, exercise extreme caution when opening emails and surfing the web!




![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
GREEN
12:38:48 2020-08-03
Yes, it couldn't be better.
Progress is evident, "all unnecessary - for scrap, collect scrap metal!"
vasvet
14:11:47 2018-07-24