More Androids, less security
Thursday, July 14, 2016
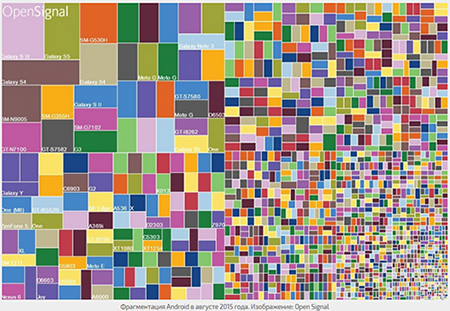
This is not a TV calibration screen. This is a diagram showing the market share of various Android devices.
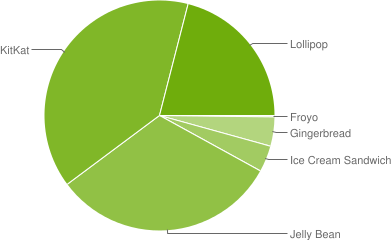
The Android platform is fragmented; each device manufacturer tailors Android for its own needs. As a result, multiple OS versions exist, and applications support devices produced by certain manufacturers rather than specific OS versions.
Similarly, with Linux, everyone can design an operating system as they see fit. Convenient? If someone intends to use only their own software, the answer most likely is “yes”. This can be good for promoting a platform, too.
But as far as security and business convenience are concerned, the prospects aren't so exciting.
Operating systems have vulnerabilities and so do the applications written for them.
Linux and Android ARE NO EXCEPTION!
Developers have to close vulnerabilities or close their offices.
What does it take to release a security patch from a development workflow point of view? The patch also needs to be tested prior to its release. Not only should it install successfully, but it also shouldn't affect the operation of other programs and services. But a developer can never know how many of those are present in the target system.
Testing always takes time and, therefore, money. And as cynical as this may sound, the testing should be done quickly because criminals may already be exploiting the vulnerability, which damages the developer's reputation to the point that customers discard the company’s software, leading to a loss in revenue. Even if the company is a monopolist.
Of course, you can do without testing; however, if something goes wrong during the patch's installation, the company will suffer from a damaged reputation and risk losing customers.
https://xakep.ru/2015/09/10/android-stats/
CVE-2014-8609 is a vulnerability that was discovered in September 2014. News of the discovery was relayed to the Android Security Team. It identified the problem, and appropriate corrections were made to the company’s main development branch. The vulnerability was officially announced in late November 2014. But…the patches for it were only incorporated into Android 5.0.
Officially, the vulnerability CVE-2014-8609 has been closed; however, Android statistics indicate that 100% of the devices are affected by it, and they will remain vulnerable for quite some time.
Some people believe that fragmentation is good since criminals can't infect all devices; the exploits they create won't be able to run on all of them. But, honestly, if your smartphone has gotten ensnared in a botnet and your neighbour's hasn't, will that make you feel any better?
Linux is as fragmented as Android. Is this an obstacle for cybercriminals?
A botnet comprised of devices running Linux reached such a magnitude that it was able to launch a 150+ gigabit per second DDoS attack, which is much more than the average corporate infrastructure can withstand. The first attacks of this kind were reported by Akamai Technologies.
habrahabr.ru/company/ua-hosting/blog/268007
The botnet used to mount DNS- and SYN-flood attacks was created by exploiting vulnerabilities in Apache Struts, Apache Tomcat, and Elasticsearch.
As many as 420,000 vulnerable devices were discovered. They were incorporated into a botnet that carried out distributed port scans for 10 months. Since implementing the project involved having to engage in illegal activities, those investigating the botnet are working undercover.
And here’s one more problem:
Google only delivers updates to its Nexus devices. Patches for other devices are the sole responsibility of their respective manufacturers. Google reported that all the information about the patches was relayed to its partners (i.e., device manufacturers) on December 7, 2015, but the actual release date for the patches remains unknown.
The Anti-virus Times recommends
- If, when choosing a new device, you are concerned with its security more than with its design, you may want to consider handhelds produced by the market leaders. Otherwise, the chances of security patches being released for your device and delivered by the manufacturer in a timely manner are slim.
- Unfortunately, you can't expect a manufacturer to continue supporting your device indefinitely. When developers design services, they either plan to update devices continuously or expect them to remain isolated, so that vulnerabilities won't be exploited.
- Since no one guarantees that a discovered Android vulnerability will be closed, device protection must incorporate a Security Auditor (available in Dr.Web Security Space for Android). It will help you prevent your device’s vulnerabilities from being exploited even if they aren't closed.


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
04:43:28 2018-08-19
vasvet
14:13:51 2018-07-24