Keep your software up to date and your systems invincible
Thursday, February 13, 2020
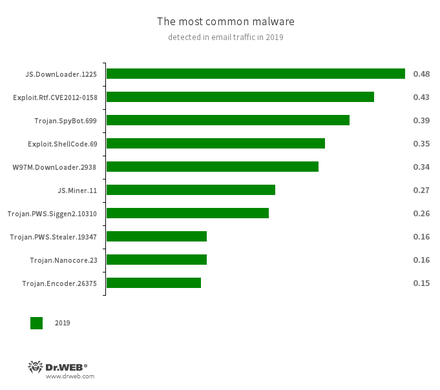
Let's see which vulnerabilities were exploited most frequently in 2019. What do last year's statistics listing the most ubiquitous malware tell us?
The second and fifth places are taken by malicious programs exploiting loopholes in office suites.
- Exploit.Rtf.CVE2012-0158 is implemented as a modified Microsoft Word document that leverages the CVE2012-0158 vulnerability to execute malicious code in a system.
- W97M.DownLoader.2938 encompasses an entire trojan downloader family that exploits vulnerabilities in office applications.
Other figures also confirm that attackers have a taste for office software.
Here is the top ten of the most widely exploited vulnerabilities in 2019:
CVE-2018-15982 – Adobe Flash Player
CVE-2018-8174 – Microsoft Internet Explorer
CVE-2017-11882 – Microsoft Office
CVE-2018-4878 – Adobe Flash Player
CVE-2019-0752 – Microsoft Internet Explorer
CVE-2017-0199 – Microsoft Office
CVE-2015-2419 – Microsoft Internet Explorer
CVE-2018-20250 – Microsoft WinRAR
CVE-2017-8750 – Microsoft Internet Explorer
CVE-2012-0158 – Microsoft Office
In sum, 3 software flaws out of 10 are found in Microsoft Office, 4 are present in Internet Explorer, whilst Adobe Flash Player has 2 loopholes. This does not mean that these programs are poorly designed. Not at all. It only shows that hackers are more likely to target common software. Microsoft Office and Adobe Flash Player are used virtually everywhere, and Internet Explorer is present on every Windows PC by default.
And, most important, these attacks remain feasible simply because users go for years without updating their installed applications.
#anti-virus_updates #security_updates #support #vulnerabilityThe Anti-virus Times recommends
- Keep your software up to date. By opening an email or a document in an outdated office suite, you are taking risks.
- Use alternatives to popular software. Even more so because Dr.Web provides anti-virus protection for all platforms.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Niuxin
22:38:11 2020-02-14
Пaвeл
20:38:56 2020-02-13
Dmur
20:33:14 2020-02-13
EvgenyZ
20:14:51 2020-02-13
Татьяна
19:49:17 2020-02-13
ka_s
19:43:09 2020-02-13
Toma
17:18:40 2020-02-13
Masha
12:33:51 2020-02-13
Неуёмный Обыватель
08:07:42 2020-02-13