Clickjacking
Wednesday, July 6, 2016
Do you trust your mouse? Unfortunately, when you click on a button or a link on the web, you can become a victim of clickjacking.
Clickjacking is a cyber-fraud technique that enables criminals to use a transparent layer placed on top of a page in a browser to carry out unlawful schemes. It is into the transparent layer that attackers load another page containing the objects they need (those may include buttons or links). Thus, clicking on a visible link or button results in actions that the attackers want to be carried out. For example, a user can subscribe to a chargeable service, make a purchase in an online store, or even divulge their confidential information. The web elements in the transparent layer can follow the cursor—thus, clicking anywhere on the page will carry out an action on another site and the user won't suspect a thing!
There was a time when the Flash player had a vulnerability that enabled criminals to use a transparent layer to activate a webcam.
Imagine someone clicking on a link on an adult site to view video content and getting photographed instantly! And after that the photo is displayed to the user with a demand to pay a ransom to get the photo removed from the database.
Clickjacking has been in use since 2008. It is used by unscrupulous companies to increase the number of visitors and likes on social networking sites, obtain personal information and even to steal online banking credentials. All they need to do is to place an invisible button on top of an existing one. And one doesn't have to be a programmer to do this. All you have to do is to contact a service offering to track your website’s visitors and get information about their Facebook profiles. They will provide you with a piece of code that you can use on your website.
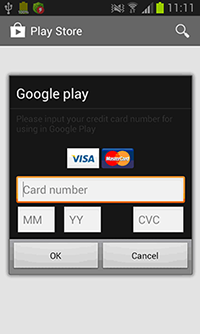
For example, if a Google Play app or certain banking applications are launched, Android.SmsSpy.88.origin displays a fake form on top of their individual windows. Once a user divulges their credit card information, the Trojan relays it to cybercriminals.
http://news.drweb.com/show/?c=5&i=9956&lng=en
The banking malware Android.ZBot lures users into divulging their logins, passwords and other confidential information by showing fake authorisation dialogues on top of the windows of other applications. The fake dialogues are downloaded from a command and control server when commanded to do so by the attackers. The fake forms imitate the look and feel of actual programs to make the user believe that a legitimate application is prompting them to enter their information.
The Anti-virus Times recommends
- Use an up-to-date version of your browser and the plugins associated with it (such as Adobe Flash Player whose earlier versions are vulnerable to clickjacking). Use the latest version of your browser with all security updates installed, regardless of what browser or operating system you use.
- Enable browser features that protect against clickjacking or install the corresponding plugins if there are any.
- When surfing the web, use a secure or private mode in your browser.
- Do not rush to click on links or buttons and launch applications on social networking sites—first, make sure that they really lead to exactly what you need.
- Use an anti-virus. Dr.Web Anti-virus and Dr.Web Security Space incorporate the Dr.Web Script Heuristics technology to prevent webpages from being modified by malicious scripts.
- • And it's not only users who should strive to maintain protection from clickjacking. Website and application developers should adopt preventive measures too. There all sorts of coding guidelines that help identify and prevent clickjacking (for example, you can check out Code Secure Block). Ознакомиться с некоторыми рекомендациями можно, например, здесь: https://learn.javascript.ru/clickjacking.


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
05:46:52 2018-07-06