More than just resident protection
Tuesday, October 23, 2018
Recently one of our subscribers wrote on social media that anti-viruses are useless and that it’s better to scan files on VirusTotal with as many as 70 anti-viruses simultaneously or opt to use Dr.Web CureIt! because it doesn't affect system performance. Unfortunately, this subscriber is not the only one who thinks this way.
This opinion exists because people don't understand how malicious programs spread and operate and how they can be neutralised. Let's look into this matter.
All modern anti-viruses have a resident module that is constantly operating in the background, tracking changes in the system and promptly responding to emerging threats. And there’s good reason for that! For example, Dr.Web has been equipped with the SpIDer Guard file monitor since the now-distant ‘90s.
Such constant control doesn't just help users who would otherwise need to scan every file they open manually but also facilitates the neutralisation of the most newly released malicious programs, which can't be detected by conventional means. The Preventive Protection is always up and running, analysing application behaviour, controlling access to system files, and promptly responding to threats as soon as they are discovered.
Of course, we are very proud of our Dr.Web CureIt! utility, but you need to understand that above all, it is an emergency curing utility that is often used after a system has already been compromised.
Let's see whether we can use Dr.Web CureIt! on its own to prevent a system from getting infected. Let's assume that you run it to scan every file you download or launch. Will it help you keep your system clean? No, and there are a number of reasons for that.
Reason #1. Malicious code can be altered to avoid signature-based detection, and the scanner won't be able to expose the threat. If a resident anti-virus module was running in the system, other mechanisms for discovering malicious activities (such as heuristic analysis) would come into play.
Reason #2. For a system to get infected, the person using it doesn't necessarily have to perform any actions with a file. Malware can sneak onto a computer by exploiting a vulnerability. That's what worms do. Remember WannaCry? The Trojan didn't need users to launch it on their computers—it scanned the network for vulnerable machines and infected them without any user intervention. The resident Dr.Web anti-virus module prevented our customers' computers from getting infected via the unpatched vulnerability.
In addition to worms, there exist bogus scripts on websites and many other covert malware deployment routines that make sure users never notice anything.
"Perhaps, you are right”—a user may say—“but scanning a computer with the anti-virus utility will expose and neutralise these threats!"
Yes, but by that time the malware may have already managed to accomplish a lot in the infected system. After all, it usually operates silently so users never notice anything. Furthermore, some malicious programs can cover their tracks by deleting modules they no longer need.
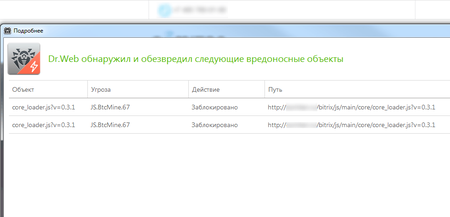
And you will be lucky if the malware you encounter turns out to be a mining script that just heats up your CPU while you’re visiting a compromised site.
Meanwhile, encryption ransomware will encrypt thousands of your files in just a few seconds. And by the time you launch the anti-virus utility it can already be too late.
The same is true for Trojans that steal personal information and passwords. The anti-virus scanner will probably detect the malware, but by then your passwords will already be on sale on an underground forum.
And what about VirusTotal and other similar sites? Of course, they can be quite useful. But malicious programs aren't always implemented as files. They can exist only as a piece of code in RAM, boot sectors, or UEFI firmware. And with no file, finding an infection on a computer may be next to impossible. And if you have no file, what will you upload to VirusTotal?
The Anti-virus Times recommends
Nowadays, many sites offer their visitors an opportunity to scan a file with dozens of anti-viruses simultaneously. Ordinary users, information security researchers, and even cybercriminals use these services. The latter do so to make sure that their Trojan won't be detected by popular anti-virus security software. But a comprehensive anti-virus solution can stop even those malicious programs that survive multiple online scanners – thanks to heuristic technologies, behaviour analysis and machine learning.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
21:07:20 2018-10-23
razgen
19:55:55 2018-10-23
vasvet
05:10:03 2018-10-23