Hey, I know these guys!
Tuesday, September 4, 2018
This sensational news report caught our attention recently:
Companies are rushing to purchase next-generation anti-virus solutions as well as software capable of detecting attacks involving bodiless malware. However, some of these companies may lack the expertise to use the tools they’ve acquired.
With over a quarter of a century of anti-virus-software-development experience under our belts, our curiosity was piqued: what are these next-generation solutions and tools capable of detecting cyberattacks involving bodiless malware? Perhaps, we got stuck in the previous century and have some catching up to do?
In any case, let us mind you that a bodiless malicious program is not some unearthly, ethereal being that leaves no traces behind in infected systems. No, it's just an ordinary Trojan, but it doesn't store its payload in a file, but in a branch of the registry (which, in fact is also a file), or it extracts its malicious code from another file before it is executed.
The malware creates several registry entries: one of them contains its encrypted body, while the other is a script that decrypts it and loads it into the memory. The names of these entries contain special characters that prevent the registry editor from displaying them.
Naturally, the more evasion techniques malware uses, the harder it becomes to detect it. But none of those techniques can make malware impossible to detect.
Despite the fact that Trojan.Kovter tries to operate secretly on an infected machine, scanning the computer with Dr.Web rids systems of this infection.
But let's get back to the news post. Here is the original article. Let's compare the texts:
The source:
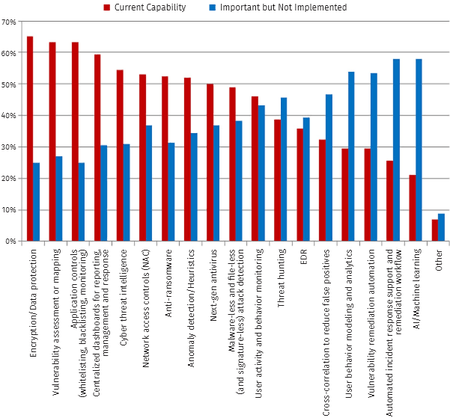
Additionally, 49% have malware-less attack detection, but 38% have not implemented the capabilities.
So we are not talking about bodiless malware but about attacks that involve no malware whatsoever. So this is how hot news topics emerge and security researchers begin to talk about new trends.
Well, then what about the next-generation anti-virus solutions?
Enhanced analysis and automation. Next-generation products will not only use machine learning but also be able to detect abnormal behaviour patterns.
"Abnormal behaviour patterns”? We've already heard about this one!
#anti-virus #technologiesThe Anti-virus Times recommends
As far as next-generation anti-virus solutions are concerned:
If you look through the features list, you will realise that application and Internet access control, as well as behaviour monitoring, are already available in modern anti-viruses.
I think that we already mentioned that "anti-virus killers" appear quite regularly, but eventually the technologies they use become part of the anti-viruses they are supposed to supersede. A similar thing may happen to popular event-monitoring and analysis projects like SIEM, EDR, and others. In any case, some people have already started referring to these systems as anti-virus solutions.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
razgen
11:27:30 2018-09-04
Неуёмный Обыватель
09:03:20 2018-09-04
vasvet
06:11:30 2018-09-04