Leaving no traces behind
Tuesday, November 21, 2017
A DDoS attack can’t happen on its own. It needs someone to order it and someone to execute it. The executor starts the attack, monitors it, corrects the list of attacked hosts, reports back to the customer on the work done, and so on.
Let's consider an attack that utilizes a botnet, i.e., a network of infected computers—this is the easiest method. During such an attack, the executors send a command to the botnet they manage, and all the computers start submitting requests to the attacked server. Each workstation has a network address. In other words, the attacked server knows the addresses of the hosts that are submitting requests to it. After analysing the report files on the machines in a botnet, one can find the PC that issued the attack command.
At first, this all seems straightforward... But why then do we know so little about criminal cases involving the accomplices of DDoS attacks?
First, a botnet itself can sometimes have issues.
Today’s botnets can be divided into two types. Botnets of the first type use command and control (C&C) servers to receive instructions, and botnets of the second type transmit information from one infected machine directly to another. Linux.Rex.1 organises botnets of the second type. These are called peer-to-peer or P2P networks. Linux.Rex.1 is a Trojan that can create P2P botnets by implementing a protocol that permits data sharing with other infected computers. Once the Trojan is launched, any computers it infects start operating as network nodes.
The malware program receives directives over the HTTPS protocol and sends them to other botnet nodes, if necessary. When commanded by cybercriminals, е Linux.Rex.1starts or stops a DDoS attack on a specified IP address.
In addition, Linux.Rex.1 is also designed to be used to transmit spam email messages to website owners, threatening to carry out DDoS attacks on their servers. To avoid being attacked, potential victims have to pay a ransom in Bitcoin cryptocurrency.
Thus, a botnet has no single point of control. Commands are sent from one computer to another. It's difficult to unravel the tangle since the computers can be located worldwide.
The second problem is the reports that tell you what addresses were used to contact the botnet’s host. The log looks something like this:
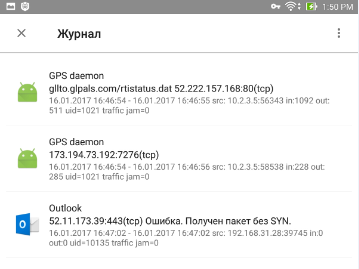
Just in case you don’t know, all the applications in this example are legal.
These reports are usually not protected, and hackers can delete them. So, any traces they’ve left behind will be erased—unless, of course, you back up your computer regularly!
Finally, the third problem. A hacker can carry out an attack not from their own computer, but remotely—from a compromised one. One that is quite possibly located in a different country, and the criminal involved can also clean up the logs.
#DDoS attack #botnet #hacking #cybercrime #securityThe Anti-virus Times recommends
- If you don’t want to become part of a botnet (and consequently—an accomplice in an attack), install security solutions; top priority: an anti-virus.
- Install updates for all the software you use—malware can penetrate different programs via vulnerabilities.
- Use strong passwords. Very often, penetration occurs after a brute force attack—and often different users have the same passwords.
- Make regular backups—this will make it easier to trace a crime if one is committed.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
07:22:35 2018-07-26
Неуёмный Обыватель
20:45:34 2018-07-25