Attacks on banking applications
Monday, May 30, 2016
For many Android users, remote banking apps are a convenient way to manage their finances. Indeed, being able to use a banking application to manage one’s finances rather than to have to always go to the nearest bank or search for the nearest ATM saves a lot of time—time that can be spent doing other, more interesting things.
Conducting transactions via such applications is supposed to be completely secure. Unfortunately, that's not the case. Despite the fact that banking institutions have made sincere efforts to make their applications secure, virus makers invent new ways to circumvent the apps’ protective mechanisms.
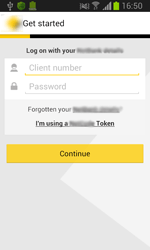
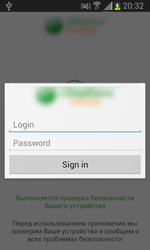
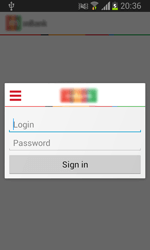
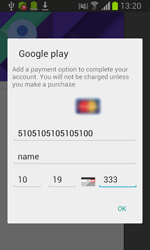
For example, a growing number of “intelligent” Android Trojans checks whether any banking software is present on the devices they infect and then stand by until the device owners start the applications. As soon as a banking app starts (Trojans can monitor the applications of dozens and even hundreds of banks), the Trojan displays a fake authorisation dialogue that prompts the user to enter their login and password in order to access their online banking account.
The dialogue usually imitates the banking app's look and feel, so most users never suspect anything. Once the user is tricked into divulging their confidential information, the latter is immediately relayed to the attackers. As a result, the criminals gain full control over the victim's accounts and can transfer money wherever they want until the user notices the theft and requests that the bank block their account or card.
Numerous members of the Android.ZBot and Android.Banker families, as well as some Android.SmsSpy Trojans, can perform the aforementioned malicious tasks.
Yet, the attackers behind Android.BankBot.65.origin went even further. Instead of investing time and effort in designing sophisticated schemes and advanced technologies, they simply took a legitimate application of a major bank and equipped it with malicious features. The tampered application remained fully operational! Criminals uploaded the compromised version to a popular site and distributed it as an update that delivered new features. They recommended that users remove the old version before upgrading. Once Android.BankBot.65.origin got onto a device, it stole information from the phone book. It could also intercept messages containing mTAN codes and reply to them to confirm unlawful transactions.
The Anti-virus Times recommends
- If possible, use mobile banking apps on a separate device, and not on the device you routinely use to access social networking sites, browse the Internet, watch video, etc. By doing so, you will reduce the risk of getting infected with a banking Trojan.
- Only install banking applications that have been downloaded from trusted sources such as Google Play or the website of the respective bank. Never install and download banking apps from other sites simply because they promise new, exciting features and superb usability. Always download programs from trusted sources.
- Make sure that you use the latest version of your banking application. Install updates as soon as they are made available.
- If two-step authentication isn’t enabled by default toggle on the option in your account preferences. If criminals gain access to your account and attempt to steal your money, you will receive a short message containing a confirmation code, and you will learn that your account has been compromised.
- Limit the amount that can be transferred using remote banking. Even if your account has been compromised, you will be able to keep most of your money, and later you will have to negotiate with the bank to return only a small amount rather than a large sum. Save your nerves!
- Use anti-virus software to thwart attacks launched by banking Trojans and other dangerous applications.


![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
16:43:18 2018-07-15