WannaCry through the mass media lens
Thursday, May 25, 2017
The tidal wave of WannaCry "epidemic" news reported by the mass media has raised a logical question: with regards to major companies and organizations getting infected, which anti-virus products have offered the best protection? Such news has interested mass media organizations, which write about topics that are of importance to their readers, and the public relations departments of the various software manufacturers.
WannaCrypt is dangerous because anti-viruses are largely unable to protect computers from it. The fact is that criminals are distributing malware capable of bypassing anti-viruses by exploiting a critical vulnerability in the SMBv1 protocol of the MS17-010 security system.
http://safe.cnews.ru/news/line/2017-05-16_analitiki_driverpack_virus_wannacrypt_vse_eshche
It's senseless even to comment on this news: everyone who read the description of WannaCry knows that the vulnerability is associated exclusively with the method of penetration. And after WannaCry has penetrated a computer, the anti-virus may well detect the files comprising it that have "popped up" in the system.
En testant la capacité des logiciels de protection grand public (avec leurs paramétrages par défaut) à détecter l’exploit EternalBlue, mis à profit par WannaCry pour se diffuser, MRG Effitas établit que seuls trois produits stoppent le code de la NSA récupéré par les auteurs du ransomware: Eset Smart Security, F-Secure Safe et Kaspersky Internet Security.
http://www.silicon.fr/wannacry-seulement-trois-antivirus-protegent-exploit-eternalblue-175315.html
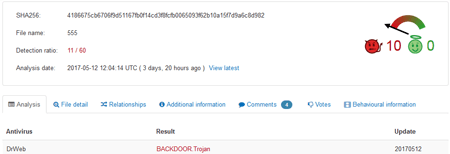
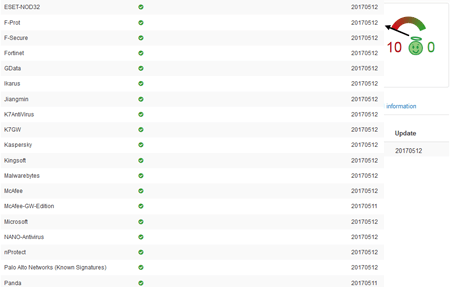
"Only three anti-virus solutions could issue a challenge to WannaCry", says the text above. Only VirusTotal showed different information:
Trojan.Encoder.11432 (also known as WannaCry) didn’t pose any threat to Dr.Web users from the moment it started spreading since it was detected by heuristic mechanisms before the first sample of the Trojan was added to the Dr.Web virus databases. It was classified as a backdoor (a remote access utility), but nonetheless it was detected and removed.
Why did a free Dr.Web solution provided by Atlant Telecom protect its users from the virus, while other anti-viruses were not able to do so?
A journalist’s question to Doctor Web’s PR service
The Anti-virus Times recommends
News is nothing more than news. Each information resource tries to be the first to report breaking news, and because of this, a situation often gets only more confusing.
Find reliable news about Trojans on websites belonging to companies that are responsible for the anti-virus security of their users.


![Shared 0 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
07:45:08 2018-07-21
Неуёмный Обыватель
03:45:04 2018-07-21