Adware predators
Friday, March 10, 2017
When users hear about viruses or Trojans on the news or in a notification from their anti-virus, they have an idea of how much danger they are in and are ready to delete threats when prompted. The same is true about spyware (spyware, key loggers, etc.). But suppose the anti-virus detected adware on your computer. Does this require any action, and, if it does, what needs to be done?
The most advanced adware can start a fight with the adware competitors that have already appeared on your computer, and destroy them. In such cases, users may never even notice the battle or other intense activities being undertaken by adware programs on their computers. And only frequent ads that get increasingly annoying can make the user realise that something has taken up residency in their system.
https://unotices.com/book.php?id=116589&page=15
Note: it is recommended that you read it out loud expressively.
If the quote above is anything to go by, one would assume that adware programs are real malware monsters, killer sharks. What are they really?
Adware is a type of software that displays ads and redirects search queries to advertising sites; it also collects all sorts of information about you in order to show you ads for goods and services that match your interests, sex, age, etc.
Because these programs promote goods and services, they are unlikely to engage in other sorts of malicious activities (e.g., log keystrokes or steal passwords). That's why adware may never manifest its presence in a system. Programs of this kind can even have an icon in the system tray and appear on the list of installed programs. They often target users who usually don't care what programs are installed on their computer, and, therefore, there is no need for them to hide.
Important! Apart from pure adware that displays ads and collects information, there exist many malicious programs that, in addition to promoting goods and services, have other features. So if ads appear on your screen, you mustn’t let down your guard—it is quite possible that your system has been infected by a dangerous Trojan.
How does adware get onto computers?
Programs of this kind are often bundled with freeware and shareware—once an application is installed, users are prompted to install other programs. That is to say that adware can be installed quite legally and this is the main distinguishing feature of these programs.
Important! Adware often doesn't incorporate uninstallation scripts and, similar to other malicious programs, it can resist attempts to remove it. There exist adware species that leave an advertising module in the system after their removal. In this case, using an anti-virus against them is quite justified.
Unlike many malicious programs, Trojan.ChromePatch.1 can infect Chrome's file: resources.pak. Attackers have been using this trick since 2015 or even longer to make sure that Chrome keeps displaying ads even after the Trojan is deleted.
- Adware can be distributed the same way Trojans are—via compromised sites. Adware that spreads in this way can fall into the Browser Hijackers category.
Why is adware considered to be malicious?
- It often fails to notify users that it’s been installed.
- It often doesn't inform users that it collects information about them.
Either of these is enough for an anti-virus to regard it as malware.
Adware is particularly common on mobile devices where most programs are free and developers can only profit from advertisements. Therefore, ads on handhelds are so commonplace that the appearance of another banner may not arouse suspicion.
In 2016, advertising Trojans and Trojans that download and install other software on devices were the most common malicious programs detected on Android tablets and smart phones.
Statistics about unwanted and potentially dangerous software provide a similar picture. In 2016, unwanted applications and aggressive advertisement modules were the most frequently detected malicious programs on Android-powered devices. The ad module Adware.WalkFree.1.origin ranked first. It was followed by Adware.Leadbolt.12.origin and Adware.Airpush.31.origin.
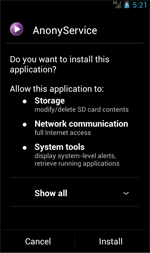
Most advertising modules for Android display banners, pop-ups, and messages on the status bar. However, many of them can also download applications and prompt users to install them.
It appears that in the coming year, Trojans and unwanted programs that display ads and download other programs without user consent will continue to increase in popularity.
Why is adware placed in a separate category and not regarded as, say, spyware?
As we already mentioned, adware is often installed with user consent and operates like legitimate programs. An anti-virus won't know whether you agreed to install this program or not—so it leaves it to you to decide what should be done about it.
When launched, Android.Spy.510 requests access to Accessibility Service. After that, it switches to standby mode and starts its malicious activities only a few days after its installation. This is supposed to reduce the probability that the user will identify the source of the unwanted activities on their infected device.
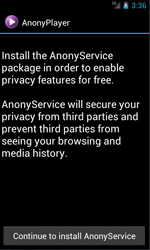
When the specified time interval has elapsed Adware.AnonyPlayer.1.origin takes advantage of the Accessibility Service to monitor system events and waits for the user to launch an application. As soon as that happens, it immediately commences executing its main task—to display ads.
Similarly to spyware, adware is hard to detect and destroy using standard anti-virus features. Although some anti-virus software developers implement features for the neutralisation of adware modules, specialised utilities that are widely available on the Internet are a better choice here.
According to this quote, adware is an invisible beast that industry giants can’t cope with but small utilities can make short work of.
There exist many adware-removal programs on the Internet.
Their main advantage is that their distribution file is relatively small.
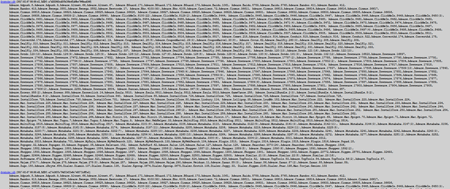
Let's take a look at updates.drweb.com. How many adware definitions were added into the Dr.Web virus database on the day this issue was being written?
And this is just for one day! After seeing that, can anyone believe that all the information about adware can be compressed into some 330 KB? There is no need to install utilities of this kind—Dr.Web detects and deletes adware as well as any other malware. #malware #Dr.Web_settigns #illegitimate_software #adware #terminology
The Anti-virus Times recommends
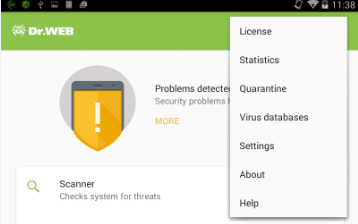
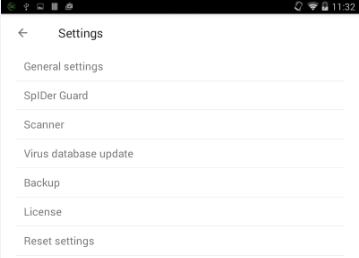
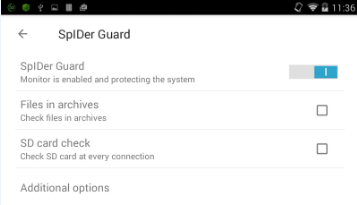
The file monitor Dr.Web SpIDer Guard is responsible for detecting adware. To access SpIDer Guard’s settings, open the application settings window. To enable the option to scan the system for adware, in the SpIDer Guard settings section, select Advanced settings. Tick the adware checkbox.


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
21:38:47 2018-06-28
azimut
00:11:31 2017-03-11
Неуёмный Обыватель
23:37:50 2017-03-10
Неуёмный Обыватель
09:01:49 2017-03-10