Non-virtual terrorism
Thursday, February 2, 2017
The scale of the threats posed by attacks on the information infrastructure of enterprises and organisations has seriously increased over recent years. It's not so long ago that using a newly discovered exploit to “nuke” the Microsoft website (as well as any other websites at hand) was considered to be more of a prank.
A company's current website is for all intents and purposes its gates to the world, and to its clients (including prospective ones), vendors, and partners, and an even ten-minute interruption in its operation can severely affect the activities of the entire company. But it’s not just websites—even a hacked Twitter account can cause problems!
The FBI has started investigating a hacker attack that petrified the whole world and whipped the news teams of hundreds of TV channels into a frenzy. On its official Twitter page, the Associated Press posted a message saying that two explosions had occurred at the White House and that President Obama had been injured. Clarification that contradicted that news followed within a few minutes, but that was long enough for all the other news agencies to pick up the hot story since the Associated Press is a trusted source of information.
As you can guess, such a hoax strongly influenced stock market prices—and the person who knew, for example, that shares in the largest US companies were soon going to drop dramatically because of the panic and then bounce back just as dramatically once the clarification was posted, made a killing.
However, such cases are rare. The most massive cyberattacks are DDoS ones (Distributed Denial of Service), and in the vast majority of cases, to perform DDoS attacks, hackers infect a large number of computers, mobile devices, and even Internet of Things devices (which are usually not protected by any anti-virus or are protected by an anti-virus of low quality) all over the world with special malware, and then use them to flood targeted websites with millions of requests, occupying bandwidth and making it difficult to use those websites.
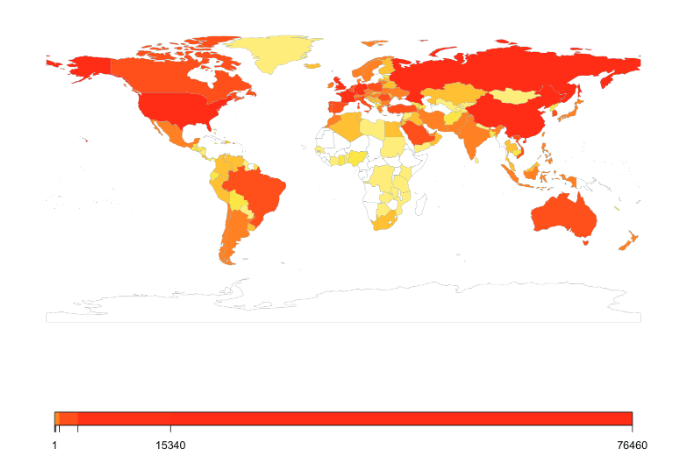
Hence, in 2016 Russia even had the sad honour of ranking first among the countries suffering from DDoS attacks—in the second quarter of 2016, we even surpassed China—and if you count up the number of attacks, Russia had about three times as many!
What’s the benefit of conducting such cyberattacks? In the case of those who carry them out, it’s totally obvious—they get money for it—thousands of dollars for a website that will be down temporarily and back up again as soon as the "employer" stops paying the hackers. But what do the “employers” get out of this? Why are they spending money on this?
The reasons can vary—from wanting to create problems for competitors to wanting to flex some muscle. But their sole overarching goal is to cause harm and TERRORIZE people.
And this cyberterrorism is not virtual. #security #anti-virus_scanning #DDoS_attack #responsibility #Internet_of_Things
The Anti-virus Times recommends
- DDoS attacks can’t last forever. They cost a lot of money for each minute of work so sooner or later they’ll fizzle out. In other words—don’t panic, which is what the cyberterrorists want, and calmly wait until the attack is over.
- Use an anti-virus to regularly scan all your computers and devices that are connected to the Internet. If a device is "smart" enough to be a potential source for cyber threats but too "stupid" to have an anti-virus installed on it, scan it remotely—for example, Dr.Web Anti-virus for Linux can scan via SSH.
- Never leave factory passwords on new computers and devices—replace them with something stronger than 12345.
- Some countries have already taken legal steps to bring the device owner who took part in the attack to justice—and rightly so!
If everyone would respect these simple recommendations, there wouldn't be any DDoS attacks!


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
05:19:48 2018-08-24
vasvet
07:24:48 2018-07-26