Shock therapy for the lazy and ignorant
Monday, January 30, 2017
Instead of an introduction, here is a short conversation:
a13x
09:23:30 2017-01-11
м...ч 

10:08:48 2017-01-11
1. (But not the most important reason) our preventive protection incorporates some really unique technologies. We know about them and tell people about them.
2. Alas, users often buy an anti-virus only, instead of a comprehensive solution that provides all-round protection—they believe that an anti-virus alone is enough. This is the true reason why we keep telling people about features that aren't present in anti-viruses only.
You are one of our regular readers (and thank you so much for your time and interest in our project), but most of our first-time visitors aren’t going to read older issues. That's why, in order to popularize vital features, we have to keep repeating information about them. What else can we do?
Even though the news is full of stories about new malware and new decryption utilities, some people may fail to notice that the IT security industry is in deep crisis.
And it's not about anti-virus products even though their development is also fraught with problems—those can be resolved. Users are the main problem.
The average user has no idea what an operating system, an office suite or an anti-virus are. And they shouldn't be blamed for that. One can be a brilliant writer, a successful manager, or an excellent mum—and none of them is obliged to be a security expert. When using their PCs and smart phones, all they usually need to do is send email and read the latest news. Of course, everyone knows that there should be some anti-virus, right?
Ordinary users don’t realise that an anti-virus alone can't provide sufficient security. Moreover, it is their genuine belief that since they've spent some money on it, the product they purchased should be able to catch all viruses.
The result is an upsurge in posts about encryption ransomware across all media outlets. Meanwhile, most of the incidents could have been prevented if only a sensibly organised security system had been in place.
What can a developer do if they want to promote products that will deliver sufficient security (so that they can at least cover the cost of developing them)? Surely, they should advertise to prospective customers. Sounds logical, doesn't it?
But even if a marketing department had an unlimited budget to place ads wherever they wanted, it wouldn't solve the problem. Are people who visit sites for expectant mothers interested in anti-virus security?
And don't forget that even employees who go through information security training will be clicking on links anyway: after all, they have to do their jobs!
How can one make users take anti-virus security seriously? There are non-trivial techniques.
Koolova is a typical encryption ransomware program. Ituses a combination of modern encryption routines, namely RSA-2048 and AES-256. It is prudent to keep system files intact to make sure that users will be able to keep using their computers. In a compromised system, Koolovvva creates the file ransom which will provide the victim with information the Trojan’s creators want to impart. And this is where things get weird.
As a matter of fact, Koolova's objective is not to extort money from people, but rather make them aware of the dangers that modern malware can present. The Trojan's makers demand that the victim read two articles about encryption ransomware — ”Stay safe while browsing” from Google Security Blog and ”Jigsaw Ransomware Decrypted: Will delete your files until you pay the Ransom” at BleepingComputer .
If the user is too lazy to read them, Koolova initiates a countdown. Should the user decline to read the reviews, the encrypted files will be deleted.
However, if they do read both publications, the decryption button Decrypt My Files (Decripta i Miei File) becomes available to them. As soon as this button is pressed, Koolova connects to its C&C server and receives a decryption key. 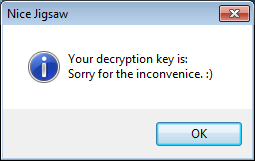
This method is somewhat similar to an anti-phishing technique that involves special emails being sent to users in order to analyse their response.
Of course, we do not approve of such methods and don't know who is behind these malware attacks, but their actions are punishable by law.
And if you were tasked with teaching security basics to users worldwide, what approach would you suggest? #security #anti_virus #encryption_ransomware
The Anti-virus Times recommends
- Take responsibility and establish usage rules for your home desktops, laptops and handhelds.
- Don't delay telling family and friends about things they shouldn't do when using a computer just because you’re feeling lazy.
- Commit some time to writing short instructions about what they should do in dangerous situations.


![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
05:17:52 2018-08-24
vasvet
19:06:19 2018-07-02
Mr.Pr
11:56:26 2017-01-31