Anti-virus pro forma 2: Problems and solutions
Thursday, January 19, 2017
In the first issue of Anti-virus pro forma, we examined in sufficient detail what happens when a company fails to protect its IT environment in a systematic way. Can companies avoid this situation and establish real security? Yes, and it’s relatively easy to do!
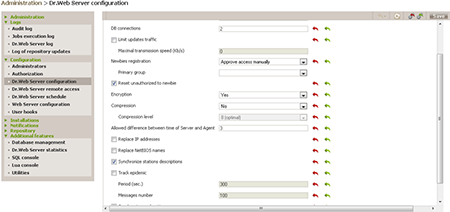
Corporate anti-virus solutions support remote administration—I think everyone understands that it’s impossible to maintain the security of dozens, hundreds, or even thousands of machines without this feature. Dr.Web incorporates this feature, too, in its Dr.Web Enterprise Security Suite Control Center (although sometimes users don't use it for reasons unknown to us, even though it is provided free of charge). Here we won't discuss all the Dr.Web Control Center features (a step-by-step guide through the basic features would occupy over 300 pages). Let's focus on how it can be used to prevent the situation we described in the first issue.
The problem
The initial infection occurred because the anti-virus on an employee's PC was either disabled or was using outdated virus definitions, allowing malware from a phishing email containing documents.exe to be launched.
https://www.ptsecurity.com/upload/ptru/analytics/Cobalt-Snatch-rus.pdf
The solution
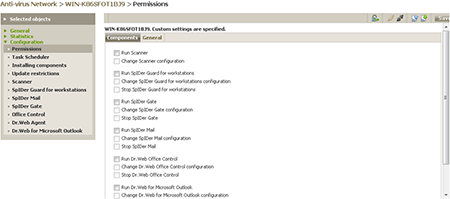
This is a simple one. First, prevent users from disabling the anti-virus.
Then configure automatic updates:
The problem
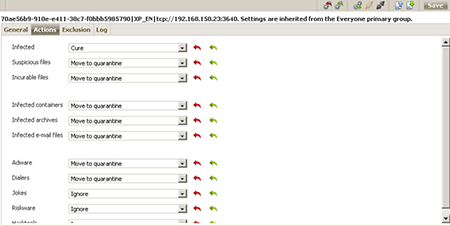
Among all the other things detected was suspicious behaviour on the part of the legitimate program Ammyy Admin.
The solution
Here the administrator could have used the Control Center to configure the anti-virus's response to malicious and potentially dangerous software:
The problem
The investigation showed that several employees had launched the files attached to the phishing emails at different times.
The solution
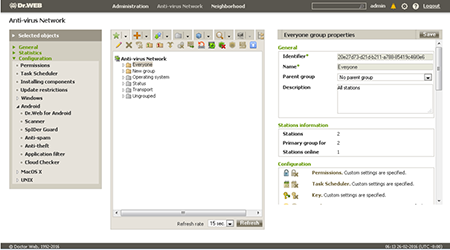
Different access permissions should have been set up for various groups of employees and individual users:
In addition, the Control Center lets you configure notifications about malware outbreaks—this will help prevent multiple infections:
The problem
To find and download various utilities (such as Mimikatz), criminals accessed legitimate sites, such as popular search engines, via the infected hosts.
The solution
Office Control, which is similar to the Parental Control that comes with Dr.Web Security Space:
The problem
An analysis of the software’s security logs confirmed that the compromised computers were engaged in network activities, including connecting to ATMs with RAdmin. Administrators in a bank network routinely use this software to remotely control network nodes including ATMs.
The solution
With the Control Center, administrator actions can be analyzed, which makes it possible to determine who is responsible for any loopholes that arise in the corporate environment. #corporate_security #anti-virus #Dr.Web_settings #Office_control
The Anti-virus Times recommends
Use anti-virus solutions properly to avoid the headaches that can be caused by unwanted incidents. More often than not, this will prevent them from happening in the first place!



![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
05:13:47 2018-08-24
vasvet
07:57:44 2018-06-30