The people who are involved and those who aren't
Thursday, January 12, 2017
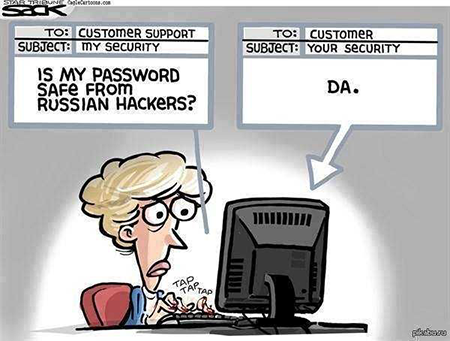
Everyone has heard about the cyber attacks that were carried out against various US organisations. If some news publications are anything to go by, Russian hackers feel right at home in America’s local networks.
But, let's get serious.
Why is there so much certainty as to the criminals' country of origin? Naturally, hackers don't want to expose their personal computers, the computers from which they control their attacks. Otherwise, the results become quite predictable and inevitable.
A Siberian hacker was ambitious enough to mount an attack on the Russian President's website. The attacker's IP address was registered by federal law enforcement agencies. Once it was established that a crime had been committed, legal proceedings followed.
A criminal investigation was started with regard to the 27-year-old Russian citizen who was accused of creating, using, and distributing malware. Now he is facing up to four years in jail.
The defendant fully admitted his guilt and did his best to assist the investigation.
Therefore, hackers need third-party PCs and servers that, even if discovered, won't put investigators on their trail. Where do hackers get such computers?
The first option—a low cost one—is to compromise another computer and use it to carry out an attack. Later, all the system logs that could indicate that the system was being used by a hacker are deleted (who protects logs?), and the attacker terminates the connection, leaving no traces behind.
Naturally, there’s a downside: suspicious activity occurring on a computer can be detected at any time by its owner or a system administrator, and then the attack will be interrupted.
The second option is for wealthier hackers. They can purchase the needed number of PCs or pay for virtual machines in a data centre.
As previously stated by American cyber security experts, six of the eight IP addresses made public by the FBI in connection with the investigation into the incident belonged to King Servers. Six of the eight IP addresses used in the attacks on the US election system belonged to King Servers.
Vladimir Fomenko, the owner of the Russian company King Servers, never suspected that the servers he rented out were being used to mount cyber attacks on the US election system.
The service is completely legal and quite popular. Who would bother to check what you are doing with servers you've rented?
King Servers: no complaints or appeals were received regarding the servers in question until September 15. No one made any attempts to seize the servers or at least contact us. Once we learnt about the problem, we disconnected the servers from the Internet immediately.
And a few words about the hackers' level of honesty: according to Vladimir Fomenko, Head of King Servers, the people who rented the servers still owe the company 290 USD. #cyber-crime #hacker
The Anti-virus Times recommends
- Trust, but verify! Are you confident that your company's servers aren't involved in unwanted activities?
- Never neglect to check the logs! Protect system messages from unauthorised modification and back them up regularly so that you can always determine an attack source.
King Servers: the fact that the attackers used our servers gives us clear evidence. Based on our log analysis, we can say that there is no way that Russian secret services were involved (unless, they hid their tracks extremely well). You see, we have all the administration panel usage logs that contain information about the activities that were carried after the hacker software was removed from the servers. We analysed the information and compiled a list of about 10 of the attackers' IP addresses. None of these addresses reside in Russia. Authorization logs indicate that the attackers logged in from addresses located in Norway, Switzerland, and Italy.
- If you conclude a server rental agreement, read it carefully, and make sure that your contractors are indeed who they say they are.


![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
05:10:05 2018-08-24
vasvet
15:12:26 2018-07-23