The steadfastness of tin soldiers
Thursday, December 8, 2016
A password is often the only thing that stands between hackers and our personal information. And there are many ways they can find it out: a password can be stolen by a Trojan, obtained during a phishing attack, or simply cracked.
Let's talk about the last possibility in more detail.
How long does it take to crack a strong password?
Remember that users generate bitcoins by means of special calculations. Nowadays, it’s ineffective to generate bitcoins at home. Those who generate this cryptocurrency are offered cloud services and specialised hardware (ASIC).
Naturally, hardware of this kind is tailored to generate bitcoins and can't be usedto find a matching password hash (a number that is calculated using special routines to make sure it will remain unique for each password) or to restore a password using a known password hash. But, for curiosity's sake, let's see what resources are available to crack passwords.
Let’s assume that all the current combined power of the devices that generate bitcoins (847, 998, 392 GH/s, ~ 10 ^ 15 hashes/sec) will be directed at cracking a password with a known password hash.
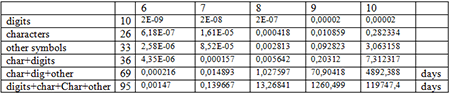
The time required to crack the hash is displayed in seconds in the table below:
It will take a day and a half to crack a password that consists of random and uppercase characters and other symbols, with a success rate of 50%. Weaker combinations require minutes and seconds.
In real life, users create predictable passwords, making the cracker’s work even easier. However, for a threat model, it is safe to assume that a 65-bit strong password will take around one day to crack (if SHA256 is used).
The Anti-virus Times recommends
Even though the example mentioned above shows that, in theory, any password can be cracked, the following recommendations are still relevant.
- A strong password is a necessity. It should contain lower and uppercase characters as well as digits and other symbols (such as +).
- Using different passwords on different sites is not merely a recommendation but a requirement.
- Passwords stored on personal computers or servers are always a pleasant surprise for an attacker.


![Shared 16 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
05:25:15 2018-08-23
vasvet
08:04:51 2018-06-30