Cyber evil tracks you by your fingerprints!
Wednesday, November 16, 2016
Data protection issues will be relevant as long as information hounds exist, in other words—always! Website and application developers, as well as gadget manufacturers, will keep trying to devise efficient technologies that make data accessible only to its owners. And this is good.
Having buried the hope that people would start using strong passwords and change them regularly, developers began promoting alternative authentication methods. And, so the biometrics era began—with fingerprint readers, retinal scans, and facial recognition.
What are the disadvantages of biometric authentication? The loss of a finger or an eye? Well, such accidents are rare. Let's consider a typical situation: a lost or stolen smartphone ends up in the hands of a curious new owner.
In recent years, lost mobile phones have been behind every fourth data leak in financial organisations in the US, and only 20% of these incidents are caused by hacker attacks. Fourteen percent of those occurred by accident, while another 13% were caused by insiders.
The problem is that fingerprints do not change. No matter how long ago we’ve left our fingerprints somewhere, they’re always ours.
A high-quality photo can be enough to reproduce a fingerprint. With certain techniques and materials, fingerprints can be reproduced to fake other people's identities. And it's not only criminals who can do this.
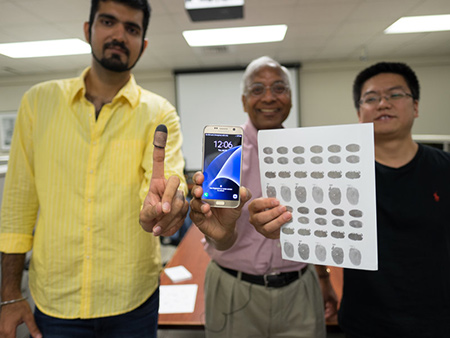
Anil Jain, a professor of computer science and engineering at Michigan State University, helped police in a murder investigation by unlocking the victim's Samsung Galaxy S6 phone which had been locked with a fingerprint. Jain and his team were able to acquire high-quality fingerprints and printed them on conductive paper (human skin conducts electricity).
By the way, our fingerprints remain on our lost handhelds too!
To authenticate a user, only some parts of a fingerprint pattern are used: e.g., ridge endings, bifurcations, and dots. Information about the morphological structure of a fingerprint is also used: the relative position of loops of papillary ridge patterns, arches and whorls. Specific features of papillary patterns are converted into a unique code. The codes are stored in a database that is used to search and compare fingerprints for matches. In some cases fingerprints belonging to different people can "match".
Papillary ridge patterns are easily damaged by small abrasions and cuts. People using fingerprint scanners at companies that have several hundred people on staff are reporting a large number of scan failures. Many scanners do not recognise fingerprints on dry skin and don't admit elderly people. At Russia’s MIPS exhibition, a security chief at a large chemical company said that their attempt to introduce fingerprint scanners (they tested scanners of various types) failed—traces of chemicals on people’s fingertips disrupted their scanners' operation, and the scanners pronounced the fingertips fake. In addition, a fingerprint image could be faked and the scanners would fail to detect it. To some extent, this has become possible due to the wide popularity of this technology. Of course, MythBusters tricks can’t be used to fool all scanners, but still. Certain people with "invalid" fingers (a slightly different body temperature, humidity) will always be denied access. The number of people experiencing this issue varies from fractions of a percent when expensive scanners are used to 10% or more when inexpensive ones are used.
Here you can find out what Myth Busters says about fooling fingerprint scanners. #fingerprint_authentication #security
The Anti-virus Times recommends
- New technologies usually make life easier, but don’t blindly trust ads that glorify innovations and rush out to buy a new smartphone. It’s quite possible that along with the benefits, you’ll get a ton of problems.
- We’re not claiming that biometric authentication is completely flawed. It is and it isn’t at the same time. It depends on what level of risk you deem acceptable. Do you store important information on your device? Is it really important? Can you simplify authentication and at the same time find another way to protect the data? These are typical questions that security experts ask, and ordinary users should ask themselves these questions, too, before choosing a security solution or purchasing a new device simply because it uses a new, hyped-up security feature. Each of us can probably recall all the many times someone in a position of responsibility promised us that everything would be fine this time.
- It’s worth understanding that the mass media strives to publish eye-catching news to attract more readers rather than provide comprehensive information on a topic. Despite high-profile stories about hacker attacks, most security incidents occur because of negligence or errors on the part of victims. A bit off-topic but nonetheless: most malicious programs are Trojans that are spread by users themselves.
Pick security solutions that match your actual needs and analyse the situation as well as the statistics.


![Shared 17 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
08:20:19 2018-07-21