False fears lead to wrong actions
Tuesday, September 20, 2016
Fake anti-viruses can't really detect and neutralise malware. Quite the contrary—they are usually nothing more than Trojans in disguise.
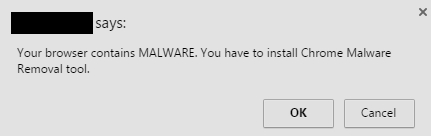
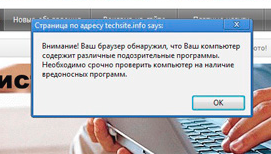
Belgian security researcher Bart Blaze discovered a new way criminals are luring people into installing a malicious Chrome extension that misleads users by claiming that their systems are infected. The researcher first came across this technique while surfing the web. On one site whose name he did not want to divulge, he saw a pop-up window notifying him about non-existent malicious programs being present in his system.
The researcher traced the origins of the window, and discovered that the corresponding script was located on a different website, not the one he was visiting. It turned out that the two sites had an agreement, according to which the first site agreed to display a third-party’s pop-up windows.
Doctor Web recommends that webmasters decline offers to host third-party scripts.
This fraud technique can hardly be called new. Similar incidents have been described in past Doctor Web publications. For example
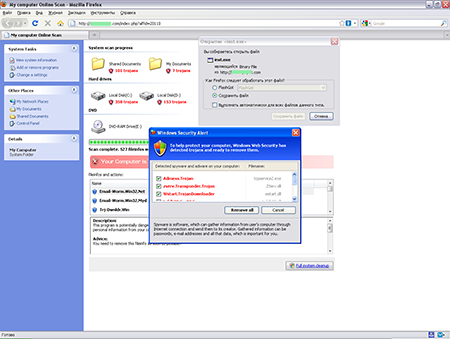
In May 2011, many media outlets published warnings about a phishing attack targeting Mac users that involved a fake anti-virus. This malware was referred to as MacDefender, MacSecurity, MacProtector or MacGuard. It got onto computers from untrusted websites that tricked users into thinking that their systems were compromised. Victims were advised to use the "anti-virus" to resolve this problem. If MacDefender was downloaded, it would pretend to search for and detect viruses, and would then set out to achieve its true goal, which was to get money from users by getting them to purchase an allegedly fully functional version.
Once installed, the program would add itself to the list of user start-up applications — Login Items. Thus, it was activated every time the user logged on or the computer was turned on. It would regularly "find" malware in the system, and always issued reminders that the malware needed to be "cured".
Criminals offered victims the opportunity to pay for MacDefender with a credit card (the credit card information was transferred through an unprotected connection). If the user paid, the program would stop detecting any malware in the system to give the impression that the money hadn't been wasted.
Under the Dr.Web classification, malicious programs of this kind belong to the category Trojan.Fakealert. Fake anti-viruses are outwardly similar to popular anti-virus software, and often their design resembles that of several anti-virus products. However, these programs have nothing else in common with real anti-viruses. Once installed, such "anti-viruses" immediately report that the system is infected (in a way, this is true), and in order to cure the infection, the user needs to purchase a full version of the anti-virus.
Fake anti-viruses are also used to spread malware. So, if, while viewing a webpage, you are notified that a malicious program has been detected and a full anti-virus scan is necessary, it is quite possible that the message is not being displayed by your anti-virus.
Fake anti-viruses regularly appear in catalogues of applications for handhelds. In such cases, they are advertised as offering 100% protection, being fast-acting, and consuming hardly any resources (which, in fact, is true because they don’t scan devices for viruses).
The Anti-virus Times recommends
- If your browser displays an infection warning, close the tab that contains the webpage. If that’s not possible, close the message window by clicking on the ‘x’ button in the top-right corner of the window. Never press buttons at the bottom of the window, below the message!
- Do not consent to dubious offers to install some new application or run an express scan. Free cheese is only found in mousetraps.
- If your computer is connected to the Internet, an anti-virus is a must-have! Dr.Web solutions make use of ScriptHeuristic technology which can perform real-time checks of all suspicious scripts loaded by your browser.
- If Dr.Web is already installed on your computer, enhance your system security with the free browser plugin Dr.Web LinkChecker – and check all links before you open them and all files before they are downloaded onto your PC, if your anti-virus isn't responding to suspicious activity.



![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
vasvet
20:58:35 2018-07-17