Tiny circuits = big damage
Friday, September 9, 2016
Home computers and other household appliances are so complex that to most users, they’re like “black boxes.” As long as they do what they’re supposed to do, how they do it is irrelevant. Well, theoretically we have a general idea of how they work, of course, but it’s rare for anyone to be able to reel off a complete list of everything a device can do (including the things that aren’t listed in the documentation).
PCs and handhelds are all around us, and there’s no telling when any one of us will fall into a criminal’s cross-hairs.
The people who look for vulnerabilities and ways to penetrate a system have both good and bad intentions. The World Wide Web is full of publications about security experts who’ve learned how to use CPU coolers to transmit passwords and how to take advantage of a handheld’s motion sensors to determine an ATM PIN code. But there exist much simpler ways to do harm to users.
Agree that it’s hard to interact with a computer if you don’t have a monitor. And everyone has heard about how hackers can intercept the contents of a CRT display. But there’s one more little detail worth mentioning. Every monitor is connected to a PC with a cable.
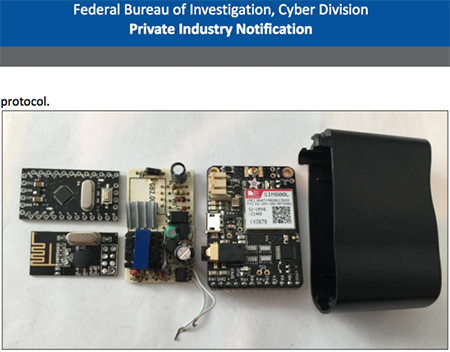
A hardware Trojan is a malicious modification, which has secretly been made to an integrated circuit, that can interfere with a computer’s operation. A hardware Trojan can render a system non-operational or disrupt its operation and provide unauthorized access to information, modify it, or remove it.
Hardware Trojans can also take the form of separate chips that criminals connect to a target system in order to achieve those same goals.
RAGEMASTER is a hardware Trojan that can intercept a VGA signal. This Trojan is concealed in a standard VGA cable connecting a video card and a monitor.
Anyone can replace a standard cable with a compromised one—and that means that criminals don’t need to sneak a camera past company security every day to photograph a monitor they’re interested in, or deploy a Trojan to take screenshots.
There are lots of places where malicious hardware can be planted.
COTTONMOUTH-II is a USB hardware implant providing a hidden channel into a target network. Designed to be connected to computer hardware, it is implemented as a dual-port USB connector. It provides a hidden communication channel that can be used to transmit commands and data between hardware and software Trojans.
COTTONMOUTH-III is a USB hardware implant that provides a wireless bridge into a target network and can be used to upload exploits onto a target machine.
Have you purchased a USB cable?
COTTONMOUTH-I is a USB hardware implant offering a wireless bridge into a target network and can be used to upload exploits onto a target machine. It provides a hidden communication channel that can be used to transmit commands and data between hardware and software Trojans. It uses a built-in radio transmitter to communicate with other COTTONMOUTH implants. MOCCASIN is the version permanently connected to a USB keyboard.
Do you use a charger for your mobile device? By default, all Android devices connect to desktops in the data transfer mode (MTP), so all the files stored on a smartphone can be accessed from a computer. And keylogger functionality can be implemented into a USB charger very easily.
You can lock your device while it’s charging; but whoever does that?
With electronic equipment getting smaller and cheaper, criminals can use technology that was previously only available to secret service agencies. We are constantly using our computers and other devices to transmit personal information, trade secrets, and personal photos. Or just chatting away on them. All of these activities are of interest to criminals and just plain pranksters.
A hardware Trojan can be implanted at any stage, starting from the design of a device to its deployment. Therefore, different detection methods are used.
If an implant is part of an original design, it is impossible to detect. At this point, an engineer can conceal or hide certain circuitry elements.
An implant can also be deployed at the production stage when an implant is introduced into the final design of a device. This method was described by InfoWorld Magazine as an April Fool's Day joke.
If criminals introduce an implant into a device when it is being delivered or deployed, it can more readily be detected. To do so, the device must be compared with an original device from the same manufacturer or with a similar device from another company. Any dissimilarities found can indicate that the device has been tampered with.
The Anti-virus Times recommends
Most users still believe that only encryption ransomware can endanger them, and they are positive that malicious programs don’t exist for Android. And although some know that malware exists for all platforms, ordinary users are completely unaware of hardware Trojans. Unfortunately, their detection requires special equipment, and an anti-virus is useless here. Therefore:
- If possible, use encryption when transferring data.
- Do not transmit data from outside of a protected environment such as your house or your company network unless absolutely necessary.
- Do not use devices or components of unknown origin.
- Remember that criminals may be seeking not only to steal information but also to alter it. Store your data in a protected storage where criminals won't be able to modify it.
While this issue was in production
Criminals can use Samsung smartphones with a locked screen.
Security researchers Roberto Paleari and Aristide Fattori published usbwatcher source code on GitHub. The usbwatcher utility can make Samsung Galaxy smartphones receive AT commands via a USB cable even if they’re locked.
http://safe.cnews.ru/news/top/2016-04-13_smartfony_samsung_mozhno_vzlomat_s_zablokirovannym
Now, to achieve their goals, criminals need only to connect a smartphone to an infected device!
Keeping your device locked while it’s charging is no longer enough.






![Shared 15 times [Twitter]](http://st.drweb.com/static/new-www/social/no_radius/twitter.png)
Tell us what you think
To leave a comment, you need to log in under your Doctor Web site account. If you don't have an account yet, you can create one.
Comments
Неуёмный Обыватель
03:49:13 2018-08-21
vasvet
07:10:10 2018-06-24
toshibasupport
11:54:26 2017-06-28